Nuclear Cybersecurity Education: A Collaborative, Multi-Format Approach Using the Asherah Nuclear Power Plant Simulator 2.0
Paul Smith, Matthew Zerphy, Gustavo Berman, Matthew Bradbury, Rodney Busquim e Silva, Khalil El-Khatib Ricardo Marques, Gary Meyers, and Hayden Nolan. Nuclear Cybersecurity Education: A Collaborative, Multi-Format Approach Using the Asherah Nuclear Power Plant Simulator 2.0. In International Conference on Computer Security in the Nuclear World: Securing the Future. Vienna, Austria, 11–15 May 2026. IAEA.
[ bibtex] [ file]
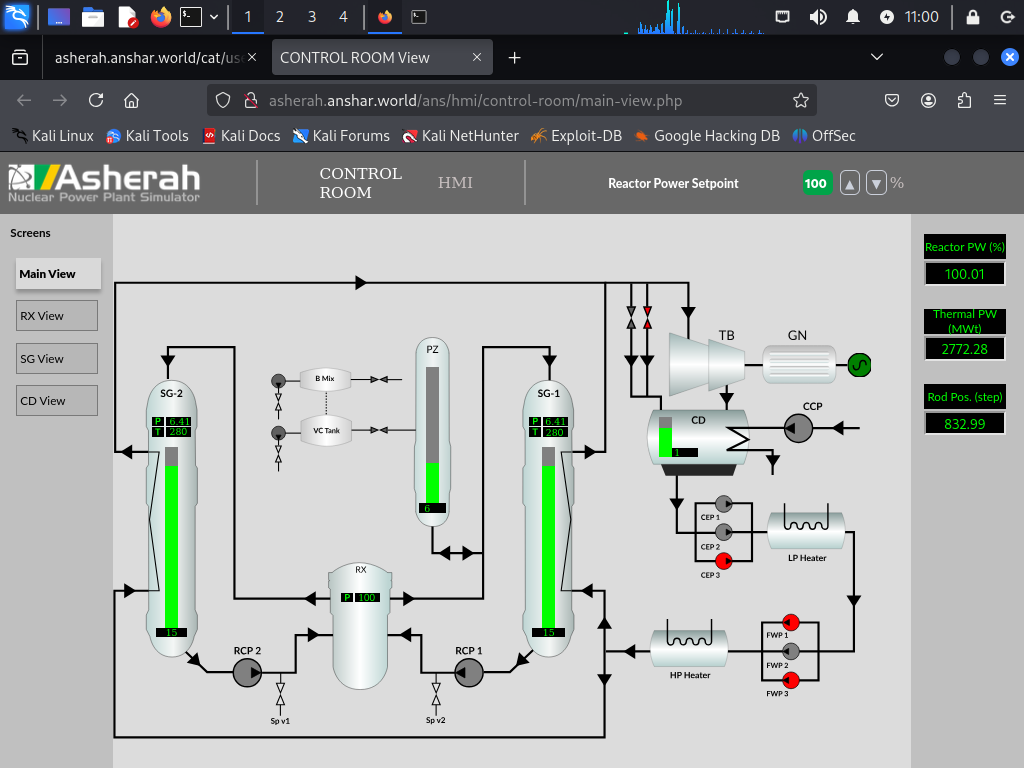
This paper presents early experiences from a multi‑institution pilot deploying the Asherah Nuclear Power Plant Simulator (ANS) 2.0 in university‑level education. Five institutions, representing diverse geographic regions, academic disciplines, and instructional formats are engaged in piloting the use of ANS 2.0 in curricula. Summaries of ongoing efforts and plans of the other three institutions piloting ANS 2.0 are also provided.
As part of Lancaster’s use of Asherah, students were given access to the internal of the simulator. This allowed them to write simple Python code to interact with OPC UA and Modbus servers. Using these scripts, students implemented attacks available within the ANS 2.0 environment, typically by writing applications that repeatedly overwrote OPC UA variables at high rates. Example attacks included manipulating reactor setpoints to values lower than those selected by the operator. Students implemented their own data historians by periodically polling OPC UA servers and storing values for all available variables in a database. These datasets were then used to implement and evaluate offline anomaly detection algorithms, including Auto Associative Kernel Regression.
Importance
Digital modernization of nuclear facilities—including advanced reactors, digital instrumentation and control, remote monitoring, and expanded networking continues to increase the cyber‑physical attack surface of nuclear facility systems. As a result, the nuclear workforce has an increasing demand for competencies that span traditional nuclear engineering, cybersecurity, and operational technology (OT). Hands‑on simulation environments complement lecture instruction to convey the tightly coupled interactions between cyber actions and physical impacts for nuclear facility operations by enabling learners to observe how cyber activities affect plant operations, demonstrate defence‑in‑depth concepts, and understand the consequences of design and operational decisions.
Perspectives
Students at Lancaster have previously gained experience interacting with vulnerable systems. However, working with Asherah allowed them to learn that there are a wide variety of digital systems in use that do not follow typical enterprise IT configurations.
Students also had to learn the importance of data gathering and analysis. The simulated physical processes gave them representative data that could be used to infer the presence of an adversary.
Finally, students needed to present their work in a format that is representative of what is required by the ONR’s outcomes-based regulatory regime. This required them to make a suitable argument about their work being appropriate and suitable.
